Why New Zealand’s Health Application Ecosystem Needs Security Baselines, Not Just Privacy Law
By Andrew Johnston | 19 January 2026
Summary
Privacy law plays a vital role in protecting patient information, but it does not define how that data must be secured.
In New Zealand’s growing ecosystem of health applications, the absence of mandatory security baselines creates systemic risk across patient portals, practice management systems, and third-party services. Recent events have highlighted why privacy compliance alone is no longer enough to protect sensitive health data.

The Manage My Health data breach has dominated headlines, social media commentary, and professional discussion across New Zealand’s health sector. Much of the conversation has focused on a single platform, its security posture, and the immediate response. This focus, while understandable, risks missing the larger issue.
The real concern is not one application, but the growing ecosystem of interconnected health platforms used by general practices, dentists, allied health professionals, and telehealth providers many of which operate outside mandatory security assurance frameworks.
The modern NZ health application landscape
New Zealand does not operate a single, unified national clinical system. Instead, health providers subscribe to a mix of Software-as-a-Service (SaaS) platforms that together support patient care, administration, and communication. These typically fall into three overlapping categories:
Patient portals and patient engagement platforms
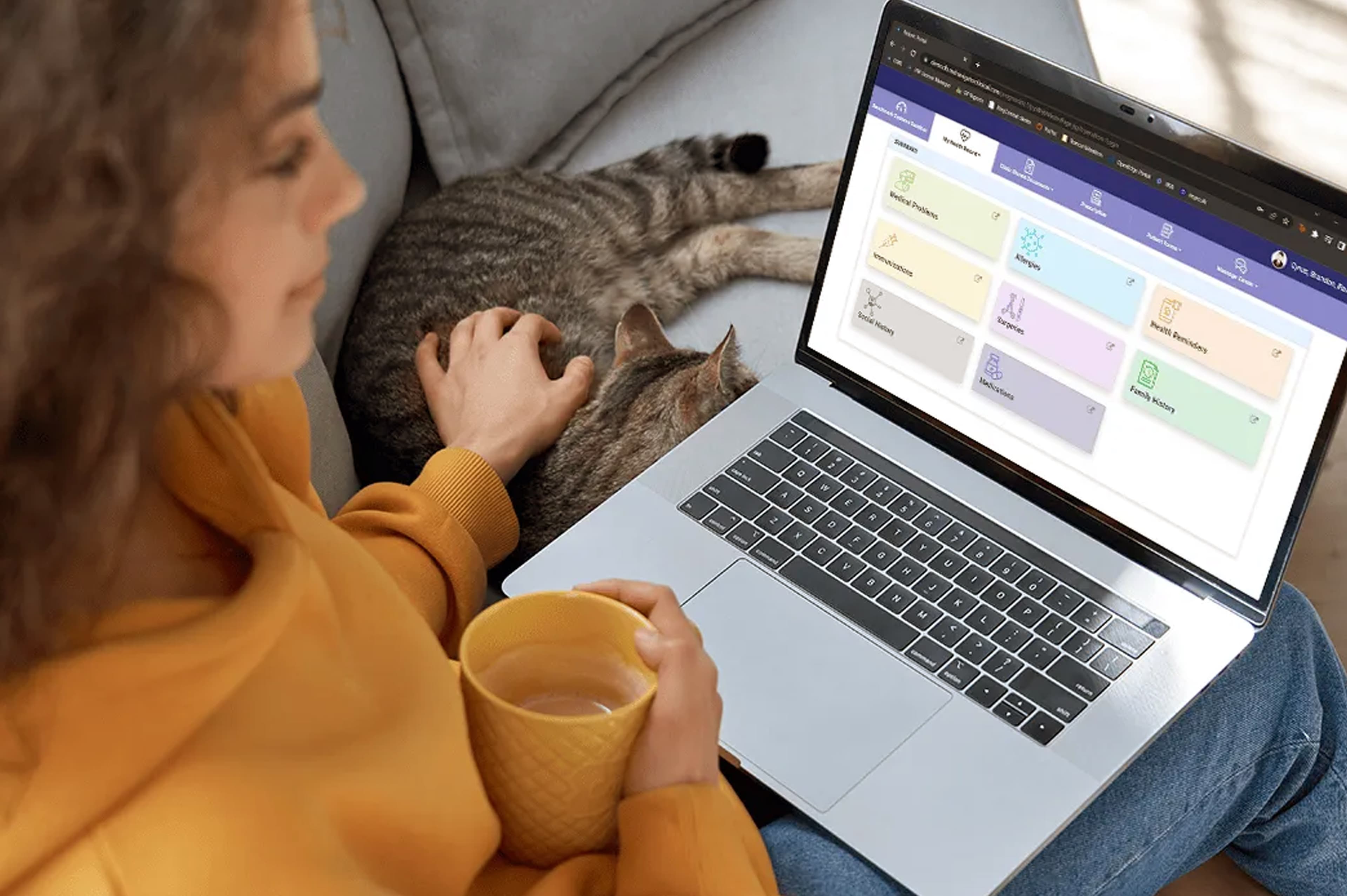
Patient portals are the most visible systems. They allow patients to log in via web or mobile applications to:
- View clinical information and test results
- Book appointments
- Request prescriptions
- Exchange messages with providers
Examples in use across NZ include platforms similar in function to Manage My Health, Health365, myindici, Centrik Patient Portal, HotDoc, and practice-specific applications.
These systems are designed for convenience and accessibility, but that same accessibility also increases exposure.
Practice Management Systems (PMS)

Behind patient portals sit Practice Management Systems (PMS). These are the operational backbone of most clinics and are used daily by clinicians and administrative staff.
PMS platforms manage:
- Clinical records
- Scheduling and billing
- ACC interactions
- Referrals and correspondence
NZ-specific PMS platforms such as Medtech Evolution, Elixir, MyPractice, Gensolve, Profile (Intrahealth), Zanda, and GoodX are widely deployed across the sector. Critically, PMS platforms often integrate directly with patient portals and third-party services, meaning that compromise of one system can cascade into others.
Third-party and telehealth services

There are supporting services such as telehealth applications, specialist referral platforms, pharmacies, and diagnostic providers frequently connect into PMS or patient portals. Even when these services appear standalone, patient data often flows back into core clinical records.
The Security Challenge
Here's where the security risks become acute: these systems don't operate in isolation.
When myindici integrates with Medtech Evolution, or when HotDoc connects to Profile, you're not just trusting one vendor's security you're trusting the API authentication between them, the data synchronisation processes, and the access controls at every integration point. This create a chain of trust risk, where the security maturity of the entire ecosystem is limited by its weakest link.
A compromise at any endpoint can expose the entire data flow. Unlike government systems where these integration points must meet NZISM requirements, health sector integrations operate without mandated security baselines.
The Legislative Double Standard
New Zealand has two comprehensive security frameworks for protecting citizen data:
- The New Zealand Information Security Manual (NZISM) published by the Government Communications Security Bureau (GCSB), provides detailed security controls covering everything from multi-factor authentication to incident response.
- The Protective Security Requirements (PSR) produced by the New Zealand Security Intelligence Service (NZSIS), binding on all government agencies.
These aren't suggestions. They're mandatory for government agencies and suppliers to the DIA Marketplace. Certification requires independent audit and ongoing compliance monitoring.
Yet the NZISM contains this critical exemption: *"Private sector organisations are also encouraged to use the NZISM."*
Encouraged. Not required. Not audited. Not enforced.
The Scale of the Inconsistency
Consider the comparative risk—Government agencies subject to mandatory NZISM/PSR:
- Inland Revenue: Tax records for ~5 million New Zealanders
- Ministry of Social Development: Benefit and employment data for a subset of the population
- Department of Internal Affairs: Identity and passport information
Health SaaS providers operating under "encouragement":
Aggregated patient portals and PMS: Medical records, diagnostic images, prescription histories, mental health notes, referral letters, and clinical photographs for a comparable scale of New Zealanders.
A breach at Inland Revenue would be catastrophic. A breach in the health sector—as we're now witnessing, can be equally damaging, with the added dimension of medical privacy violations that can cause lasting psychological harm, embarrassment, and discrimination. Yet only one sector faces mandatory security controls.
The health sector does operate under privacy frameworks:
- Privacy Act 2020: Establishes principles for handling personal information
- Health Information Privacy Code 2020 (HIPC): Specifically addresses health information
- Retention of Health Information Regulations 1996: Governs record retention
These frameworks mandate that data must be protected. They don't prescribe how to protect it.
Principle 5 of the HIPC requires organisations to "protect personal information by security safeguards that are reasonable in the circumstances." But what's "reasonable" for a small GP practice with limited IT expertise? Without technical guidance or mandatory baselines, we're relying on each provider to interpret this independently.
The NZISM provides precisely what's missing: specific, auditable controls such as:
- Multi-factor authentication requirements** (NZISM 17.1.46)
- Security event logging and monitoring** (NZISM 16.6.9)
- Incident response capabilities** (NZISM 16.5.37)
- Access control frameworks** (NZISM 17.1)
- Vulnerability management** (NZISM 17.3)
These aren't theoretical. They're proven controls that government agencies implement daily to protect citizen data of comparable sensitivity.
Why Does This Gap Exist?
The inconsistency appears to stem from policy evolution rather than deliberate design. When NZISM and PSR were developed, the focus was on government agency accountability. The assumption may have been that sector-specific regulation (like HIPC) would address private sector needs.
But the health technology landscape has fundamentally changed. What were once locally managed practice systems are now cloud-based SaaS platforms operated by commercial vendors, often with offshore data storage, third-party integrations, and complex supply chains.
GP practices, dental clinics, and allied health providers are generally small organisations without dedicated security specialists. They're clinical experts, not cybersecurity professionals. Expecting them to independently assess the security posture of their SaaS vendors, evaluate integration risks, and implement defence-in-depth strategies is unrealistic.
About Liverton Security
Digital technology has greatly expanded opportunities for businesses, but has also introduced complex security threats that organisations cannot ignore. Protecting people, critical data, and entire organisations requires proactive and continuous security strategies.
As an influential and respected leader in global cybersecurity, Liverton Security specialises in helping businesses and government organisations neutralise evolving cyber threats in the digital age.